Here’s my rundown of Tr0ll:1, a boot2root on Vulnhub that I had some fun with a few weeks back. I did feel like I was being trolled as I went at it and there were moments where I nearly needed to order a new keyboard but nevertheless, it was great fun when I finally got there.
I booted the VM and ran nmap -sn to find the IP. Then followed the port scan.
3 ports with the usual suspects running on them. Three things that I noted were the anonymous FTP login, a writeable file and a /secret page that might be worth looking into. I started with a quick look at the web page.
Love it. Let’s go straight to the /secret.
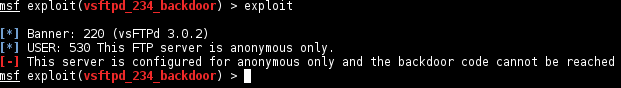
Not mad yet, mildly amused. There was nothing in the source of these pages and I didn’t want to DirBust it unless it’s a last resort, so I left it and went for VSFTPD. Before connecting directly I recalled a Metasploit module for this I saw a while back. I didn’t expect it to work but hey, it’s worth a try for all of the 10 seconds it would take.
Ok, so apparently anonymous is the only way into it. Let’s see if we can find that file.
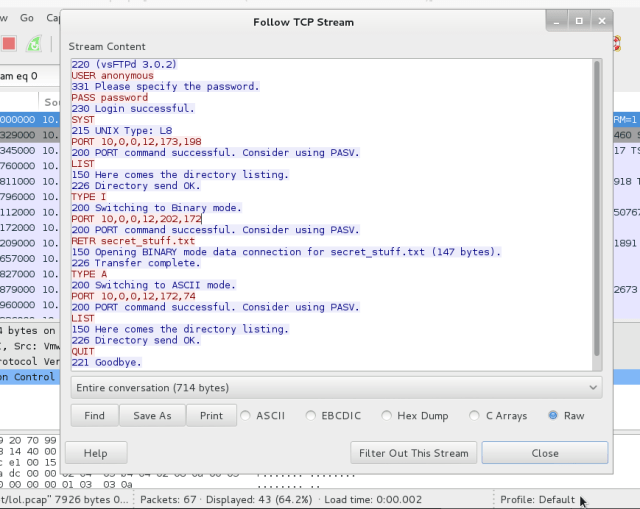
Let’s load up Wireshark and see what’s in the pcap. I followed the TCP stream of the first packet and found the following.
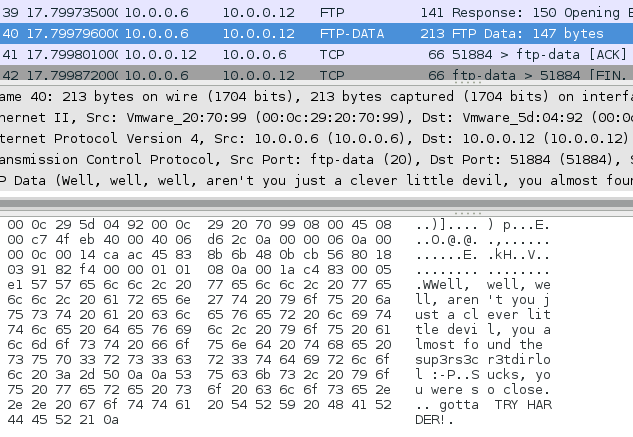
What’s that I see… secret_stuff.txt ? Thanks muchly. I then spent an embarrassing amount of time bashing my head on the keyboard running the above and various other commands in my FTP window to try and find the secret stuff, all to no avail. Only to realise that the data I needed was right in front of me in Wireshark…. >_>
Ooo, sup3rs3cr3tdirlol? Let’s gogogo.
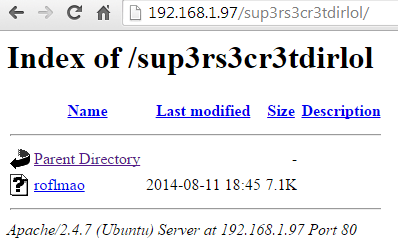 I downloaded roflmao and had a cursory glance.
I downloaded roflmao and had a cursory glance.
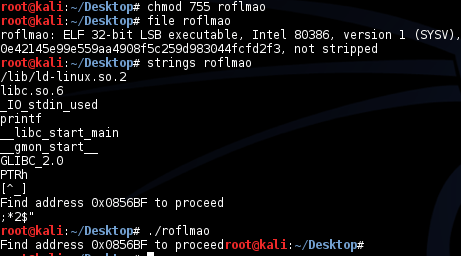 So it’s an executable that tells me to find an address to continue. As it was a hex address the forensic sleuth in me instantly thought “offset within the file”. Here we go, onto winner here 😀
So it’s an executable that tells me to find an address to continue. As it was a hex address the forensic sleuth in me instantly thought “offset within the file”. Here we go, onto winner here 😀
Oh, the file isn’t large enough to contain that offset. I won’t lie I got stuck here for a while until I had what drunks refer to as “a brief state of clarity” and re-read the clue, “Find address 0x0856BD”.
Right now we’re getting somewhere. “which_one_lol.txt” contained what appeared to be a list of usernames shown below…
maleus ps-aux felux Eagle11 genphlux < -- Definitely not this one usmc8892 blawrg wytshadow vis1t0r overflow
…and “Pass.txt” contained the following:
Good_job_:)
Schweeeet. A simple brute force of users with the password! I added the list of users to a file and ran Hydra with it, shortly after which I was getting errors. It seemed like there were some throttling of sorts going on to limit my connections. I got stuck here again for a while until I (probably for the 174th time) went back to the /0x0856BD page and looked again at the contents. Trying to think a bit more laterally again I looked at the folder “this_folder_contains_the_password” and thought maybe it literally does. So I ran Hydra again with the same users but this time setting the password to Pass.txt

SUCCESS!
We’re in. As overflow albeit it, but we’re in. Now to try and escalate our privileges. I started poking around and I couldn’t see terribly much of interest and then….
 Something kicked me out. I logged back in and quickly searched for all world writable files.
Something kicked me out. I logged back in and quickly searched for all world writable files.
find / -perm -0002 -type f -print 2<dev/null
(For the record there’s a very nice script called LinEnum written by a colleague of mine that enumerates a plethora of useful information about Linux and can identify security mis-configurations in one go)
This resulted in a long list of files, one of which stood out like a sore thumb:
/lib/log/cleaner.py
This file contained the following:
 Bingo. I first tried editing this to cp /root/flag.txt /tmp/ but it didn’t work and realised the flag may not be called ‘flag’. So rather than guess a few other likely file names and risk actually getting it right, I wanted to get my own root shell to do it properly:
Bingo. I first tried editing this to cp /root/flag.txt /tmp/ but it didn’t work and realised the flag may not be called ‘flag’. So rather than guess a few other likely file names and risk actually getting it right, I wanted to get my own root shell to do it properly:
Went to make a coffee with an optimistic smirk on my face whilst I waited to be kicked out again. Then I logged back in, ran my new shell, and looked for the loot.
WIN.

LIKE A BOSS